Security Built on Intelligence. Insight Designed for People.
Secure Passage delivers Operational Intelligence that helps organizations understand their environments, strengthen decision-making, and protect what matters most. Our solutions bring together video, sensors, access, behavior, and device activity into identity-aware insight—creating a clearer, smarter picture of what’s happening and why it matters.
From schools and enterprises to critical operations, data centers, and large-scale properties, each deployment is shaped around your world: your workflows, your infrastructure, your mission.
Complexity becomes clarity. Signals become understanding. Insight becomes action.
Your Tools. Working for You.
Most security teams end up working for their tools—staring at video walls, chasing alerts, and sorting false alarms. Truman changes that. It turns your environment into identity-aware intelligence, correlating video, sensors, access, movement, and context to reveal who or what is present and why it matters.
Truman captures the physical-world attributes IAM has never had—biometric cues, license plates, MAC signatures, device patterns—and uses AI to detect anomalies, connect behavior, and elevate what deserves attention. It even tracks activity across your machine ecosystem, showing how applications and AI agents operate, what they touch, and the signals they leave behind.
Instead of drowning in data, Truman helps your tools think together—and point you toward the moments that count.
It’s not just awareness—it’s Operational Intelligence that makes identity meaningful and decisions smarter.
About TrumanSituational Intelligence With Real-World Impact.
When incidents surface, teams often struggle to connect signals across people, places, and events. Haystax brings everything into one view—uniting reports, tips, system alerts, environmental inputs, and operational data into a single, contextual picture of risk. It highlights what matters, suppresses the noise, and helps organizations act sooner and more confidently.
Built for school safety, statewide operations, critical infrastructure, and event risk missions, Haystax gives teams the clarity to see emerging patterns and the structure to coordinate response across agencies and stakeholders.
Instead of piecing data together under pressure, Haystax delivers the context needed to stay ahead of threat, complexity, and uncertainty.
It’s not just visibility—it’s situational intelligence built for real decisions in real time.
About HaystaxSafety Through Insight.
Most organizations rely on fragmented notes, disconnected emails, and siloed workflows to manage behavioral concerns. BTA brings order to the process—centralizing reports, histories, observations, and follow-ups into a structured, collaborative case framework that helps teams see the full picture sooner.
Built for schools, enterprise HR, and healthcare environments, BTA supports multidisciplinary teams with clarity, consistency, and documented accountability. It aligns people and process while contributing valuable context to identity-aware operations across your broader security ecosystem.
Instead of missing key details, BTA helps teams track, evaluate, and act with confidence and care.
It’s not just case management—it’s a safer, more informed way to support people and prevent harm.
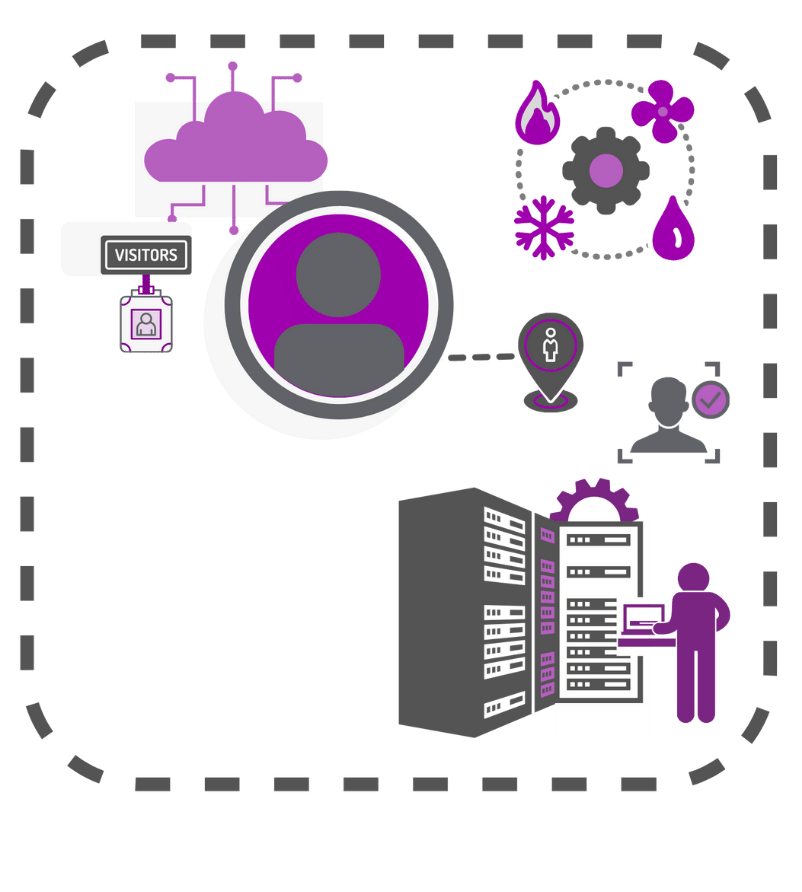
About BTAIdentity Assurance for High-Security Environments.
In data centers and critical facilities, identity gaps create operational, compliance, and risk exposure that traditional access control can’t solve alone. Vigilant unifies identity, access, environmental signals, and policy requirements into a single layer of assurance—showing who is present, what they’re doing, and whether their behavior aligns with expectations.
Built specifically for data-center operations, Vigilant strengthens governance programs with continuous validation, clean audit trails, and real-time insight across employees, visitors, and contractors. It reduces friction, tightens control, and supports Zero Trust alignment for the physical side of identity.
Instead of relying on fragmented logs, Vigilant turns identity activity into clarity you can prove and decisions you can trust.
It’s not just compliance—it’s the confidence of knowing identity and access always match.
About VigilantTaming the Data Beast.
Organizations generate more physical and digital signals than any team can interpret alone. Dragon solves that by ingesting, normalizing, and organizing massive volumes of raw data—turning noise into clean, structured, operationally useful intelligence.
Dragon strengthens every Secure Passage solution by filtering out low-value events, revealing meaningful patterns, and reducing storage, compute, and personnel overhead. It becomes the foundation that identity tools, situational awareness, and operational workflows rely on to perform at scale.
Instead of drowning in data exhaust, Dragon gives teams a clear, dependable layer of understanding that makes every other system smarter.
It’s not just aggregation—it’s the engine powering Operational Intelligence.
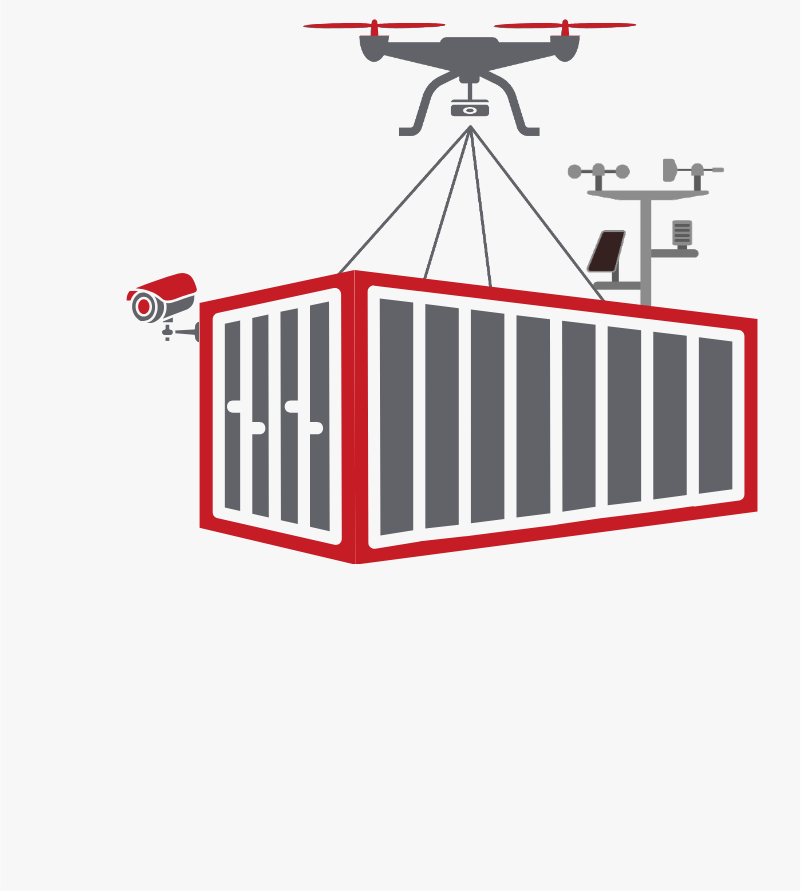
About DragonDeployable Intelligence for Any Environment.
Some environments can’t support permanent infrastructure—large properties, outdoor venues, temporary perimeters, remote sites. Apex brings Operational Intelligence to all of them through a rugged, mission-configurable station that delivers real-time visibility wherever the moment demands it.
Built to adapt, Apex supports a customizable mix of video, sensors, communications, and environmental analytics. It extends awareness beyond fixed systems, capturing the presence, movement, and activity signals that complete the physical picture surrounding identity and operations.
Instead of accepting blind spots, Apex brings clarity, reach, and response capability to places traditional systems can’t go.
It’s not just portable hardware—it’s deployable Operational Intelligence.
About ApexExpertise That Moves Your Mission Forward.
Security programs are only as strong as the strategy behind them. Strategic Services brings advisory clarity, technical integration, and mission-aligned support to help organizations strengthen what they have—and build what they need. From identity alignment and workflow design to sourcing and engineering, our team helps create security ecosystems that work together instead of working against each other.
Whether modernizing a legacy environment or guiding a new deployment, Strategic Services turns complexity into a clear, sustainable plan shaped around real-world requirements.
Instead of navigating the landscape alone, you gain a partner who understands your mission—and builds to fit it.
It’s not just support—it’s expertise with measurable impact.
Strategic Services